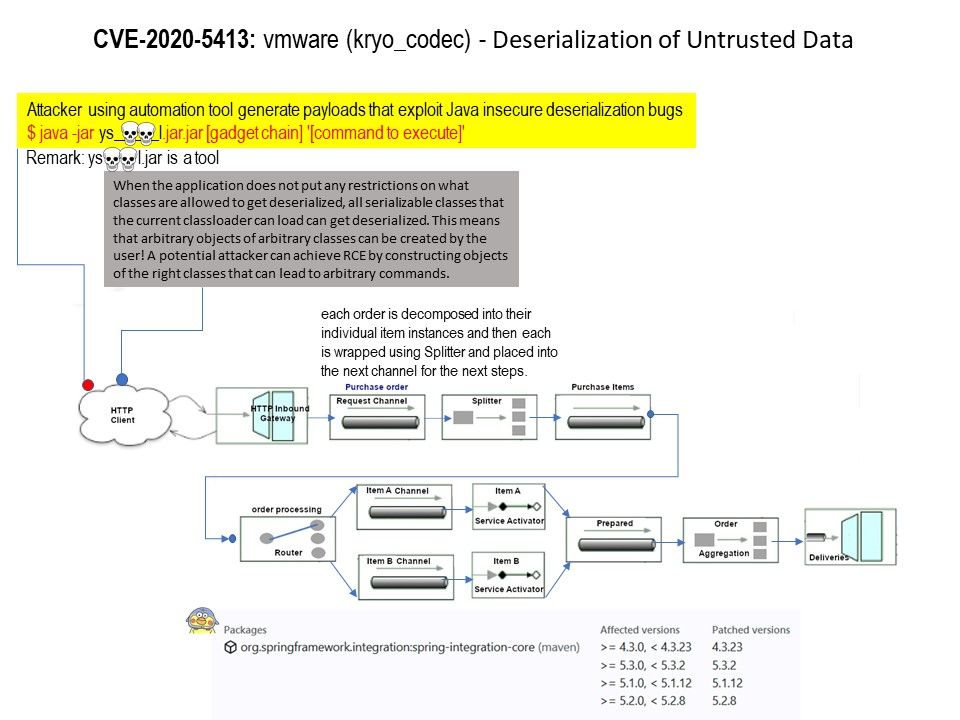
CVE-2020-5413: vmware (kryo_codec) – Deserialization of Untrusted Data (Aug 2020) | Cyber security technical information
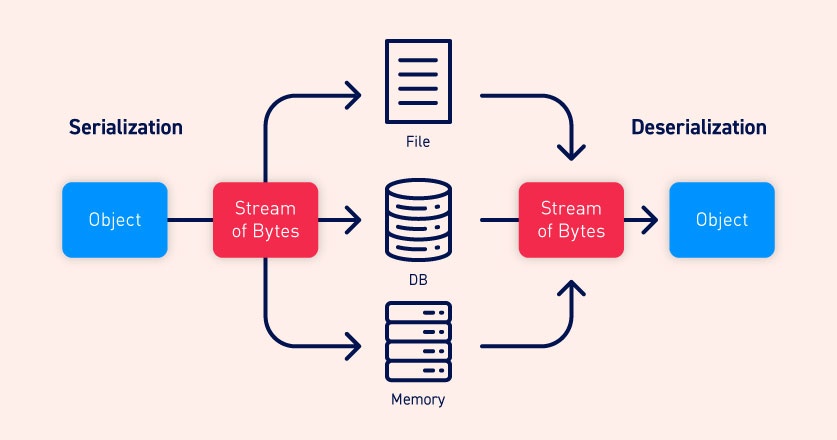
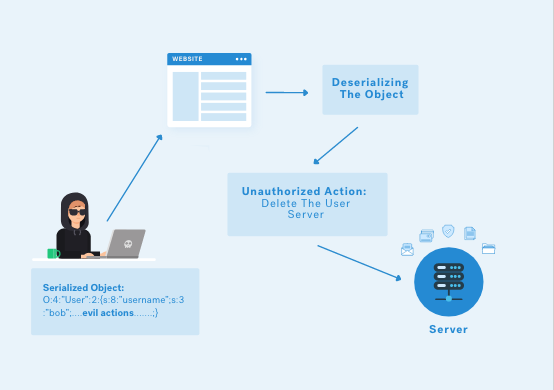
Dealing with Deserialization of Untrusted Data in Java Applications - GBHackers - Latest Cyber Security News | Hacker News
Dealing with Deserialization of Untrusted Data in Java Applications - GBHackers - Latest Cyber Security News | Hacker News
Dealing with Deserialization of Untrusted Data in Java Applications - GBHackers - Latest Cyber Security News | Hacker News

SSD Advisory – Microsoft SharePoint Server WizardConnectToDataStep4 Deserialization Of Untrusted Data RCE - SSD Secure Disclosure