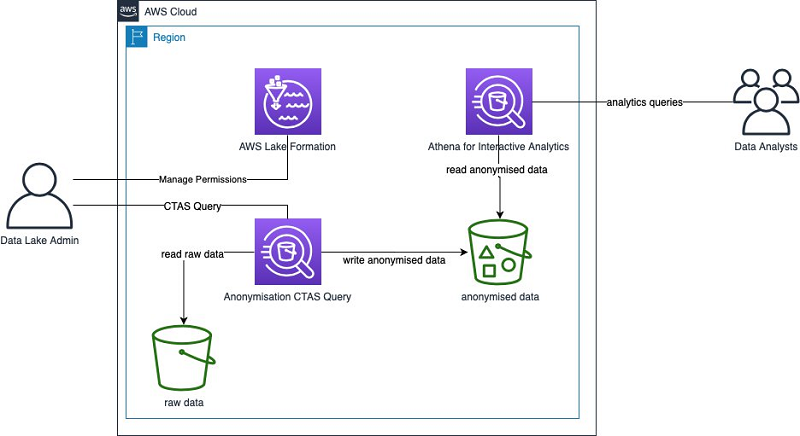
Anonymize and manage data in your data lake with Amazon Athena and AWS Lake Formation | AWS Big Data Blog

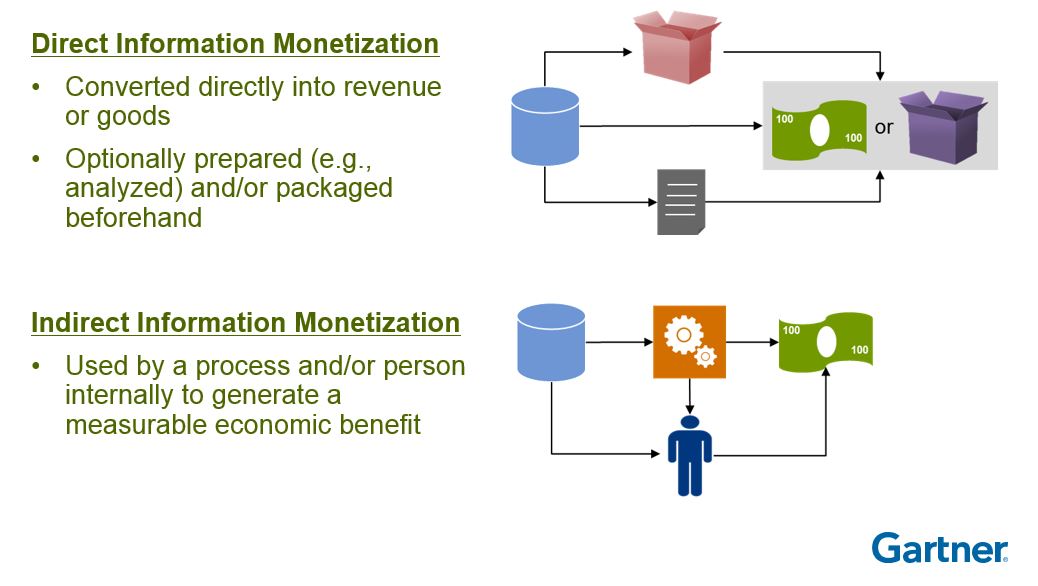
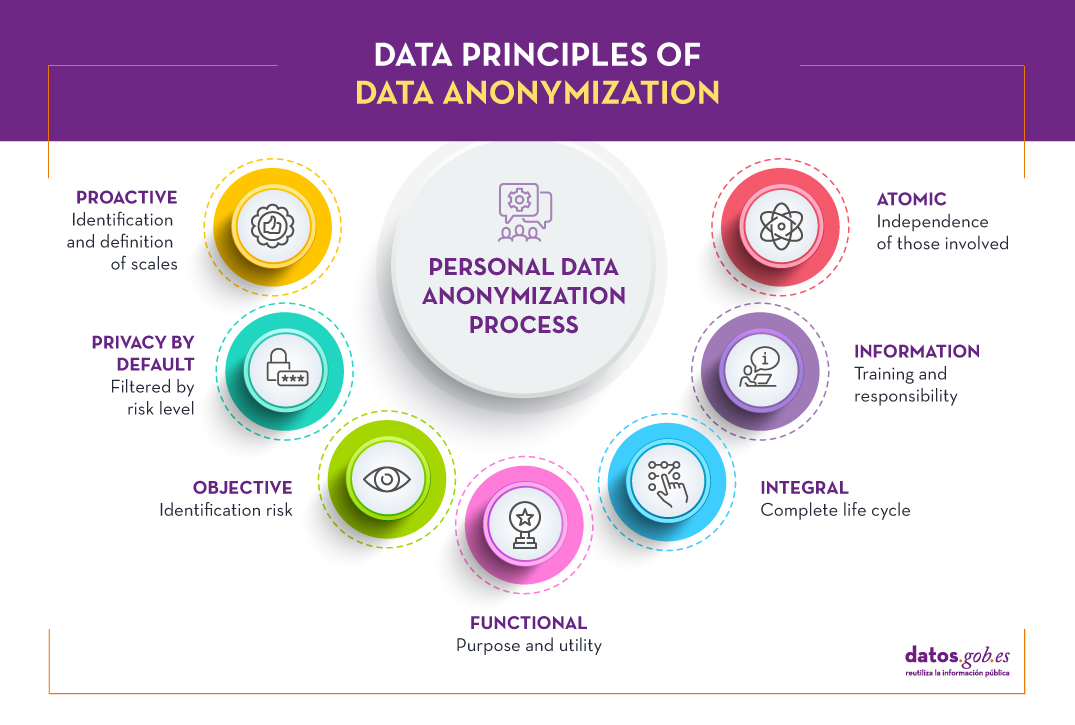
Data Anonymization Techniques Ppt Powerpoint Presentation Slides Example Cpb | Presentation Graphics | Presentation PowerPoint Example | Slide Templates