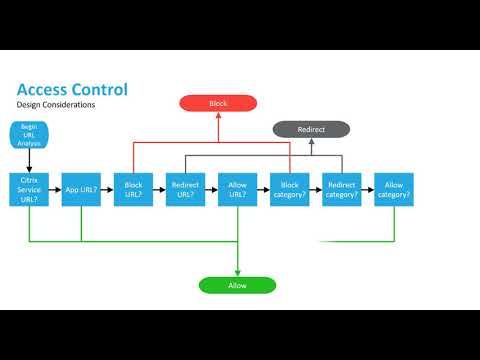
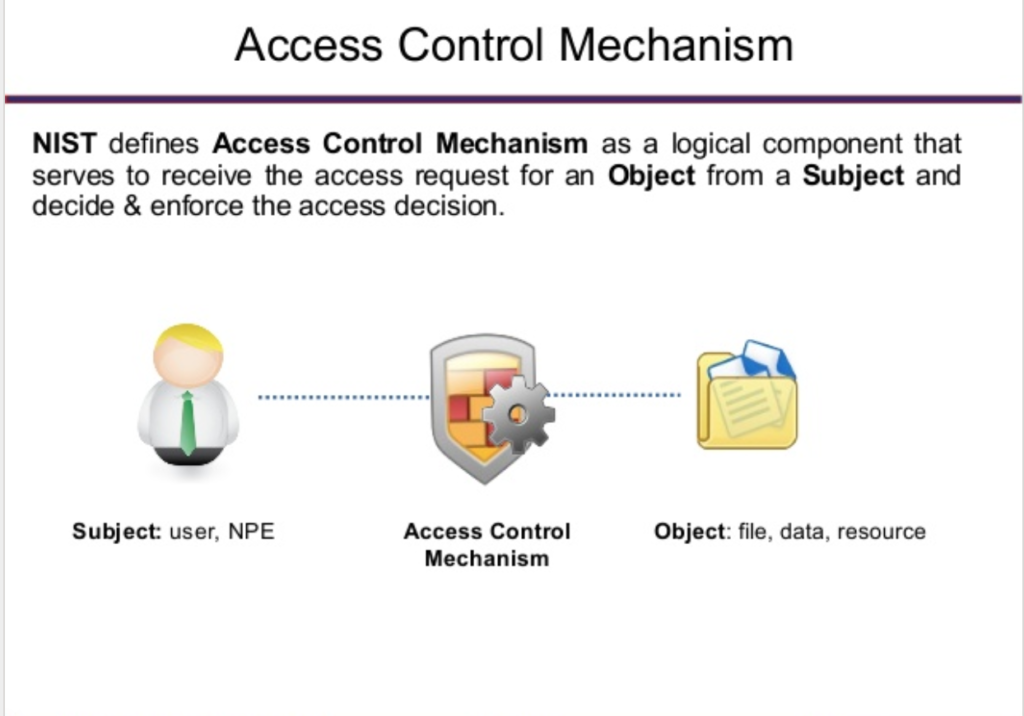
Global Access Control as a Service Market - Growing Awareness About Sophisticated Data Security Threats Drives Growth | Technavio | Business Wire

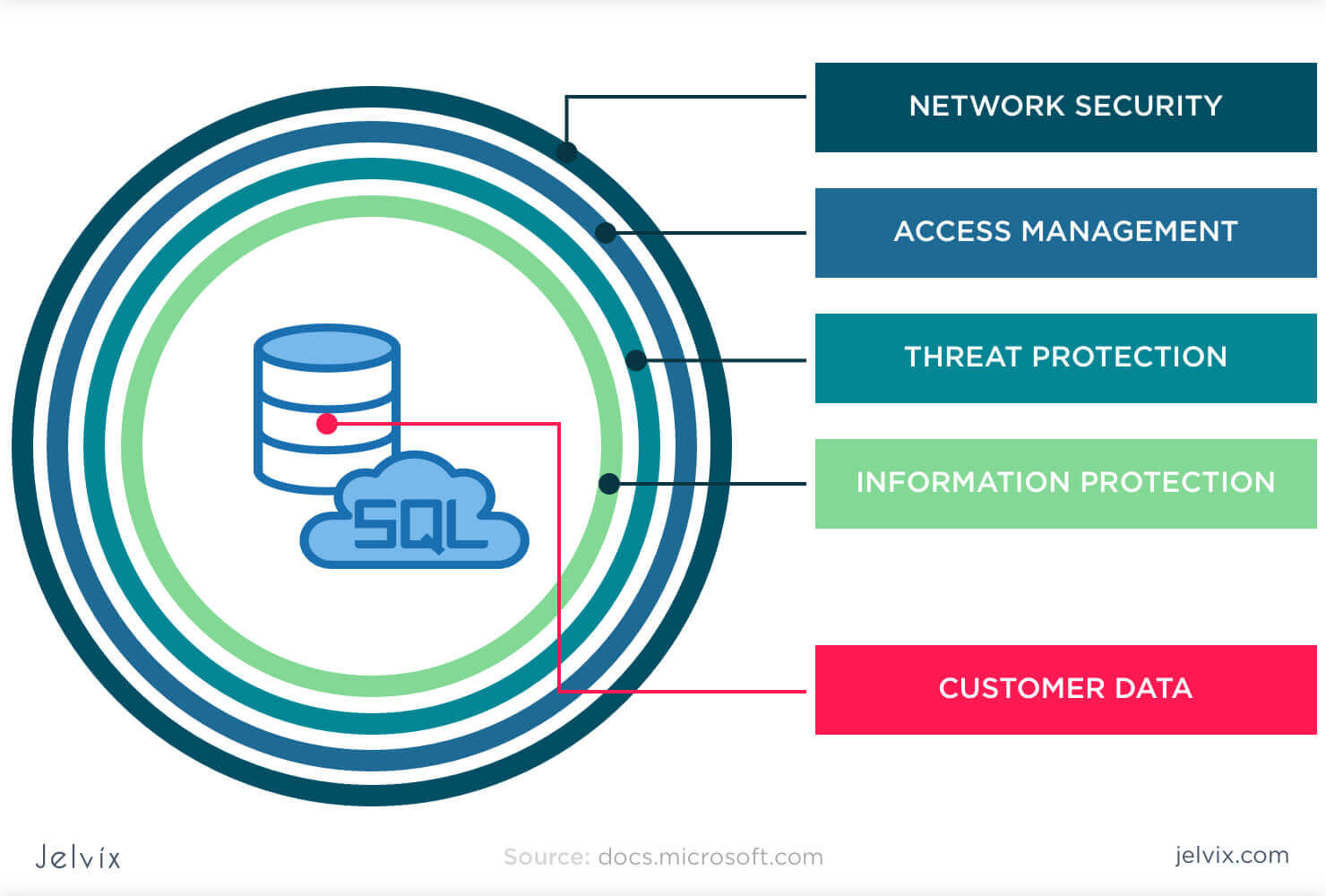
It's Not Just YOUR Compliance That Matters: Tips for Ensuring Third-Party Data Security DonorPoint -

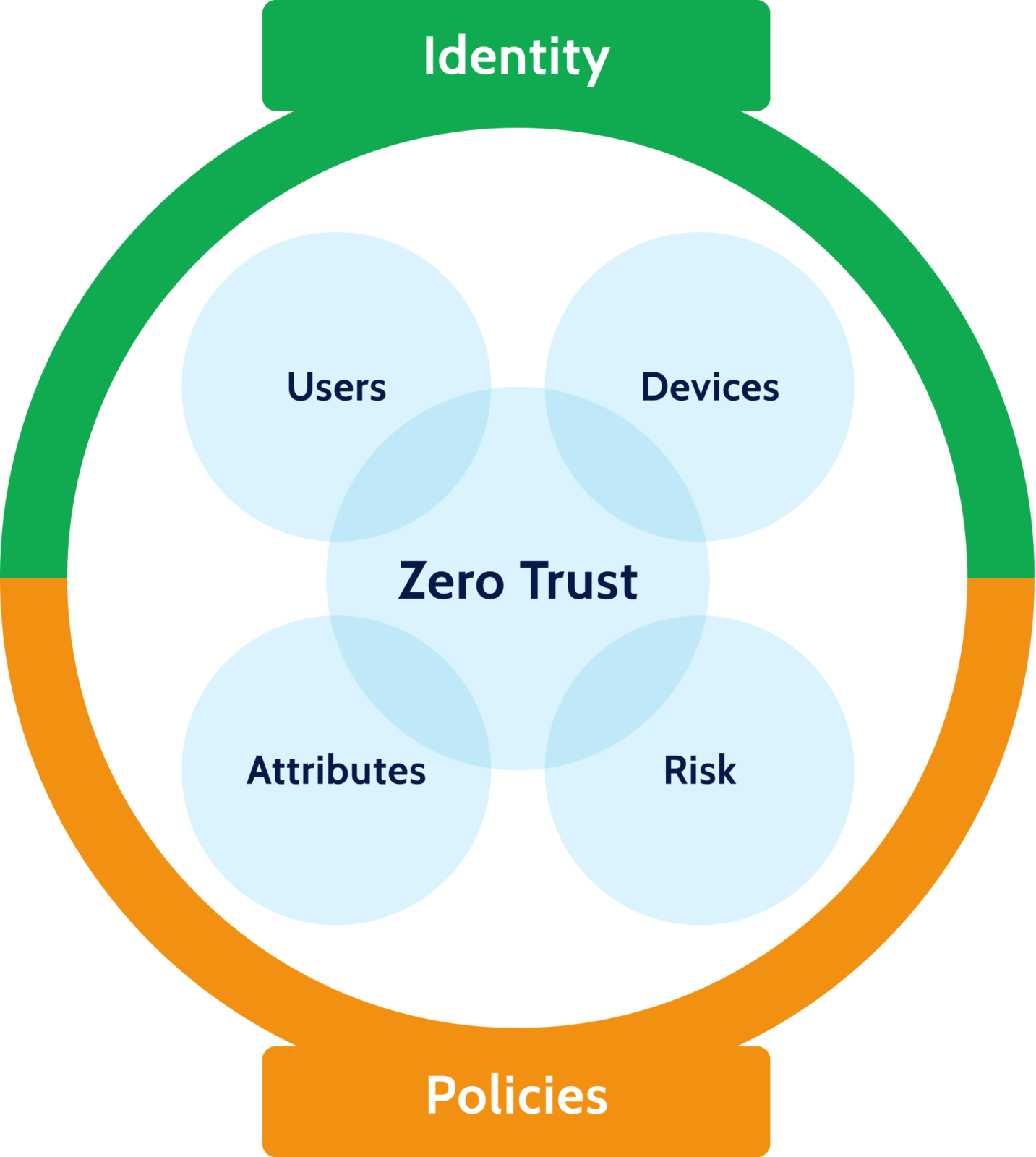
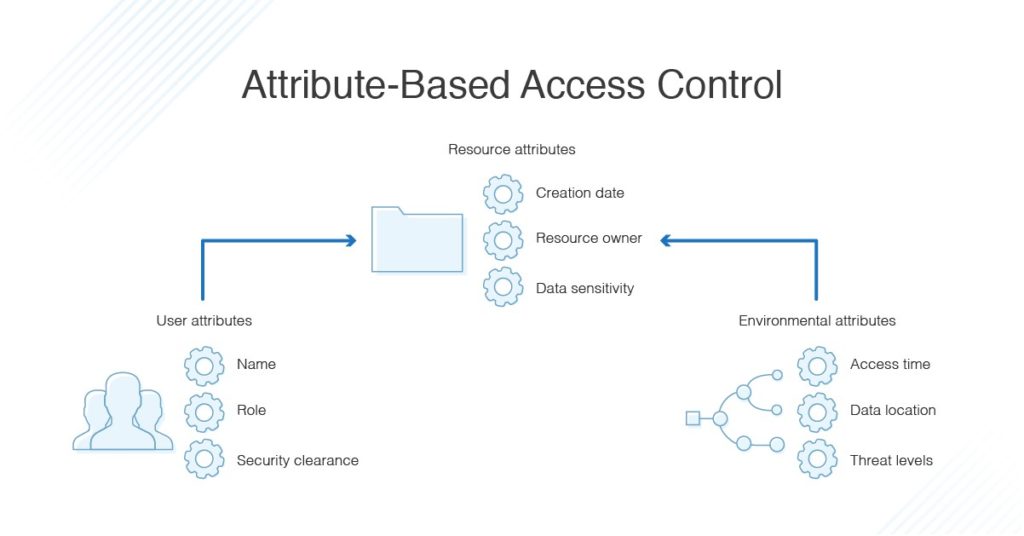
Attribute-based data access control in mobile cloud computing: Taxonomy and open issues - ScienceDirect